With the PoSH script made available through this blog post you can scan and check ALL accounts in the AD forest to get “Account And Password Hygiene” related information.
Through LDAP queries, this PoSH script retrieves the following information for every account in the AD forest that is able to authenticate:
- Domain FQDN (e.g. ‘IAMTEC.NET’)
- Domain NBT (e.g. ‘IAMTEC’)
- Domain DN (e.g. ‘DC=IAMTEC,DC=NET’)
- Sam Account Name (e.g. ‘jorge’)
- Account Name (e.g. ‘IAMTEC\jorge’)
- Account Type (computer, inetOrgPerson, msDS-GroupManagedServiceAccount, trust (user), user)
- Enabled (e.g. TRUE or FALSE)
- Pwd Last Set On (e.g. <date/time> or "Must Chng At Next Logon")
- Has Adm Count Stamp (e.g. TRUE or FALSE)
- Delegatable Adm (e.g. TRUE or FALSE)
- Does Not Req Pre-AuthN (e.g. TRUE or FALSE)
- Has Sid History (e.g. TRUE or FALSE)
- Has LM Hash (e.g. TRUE or FALSE)
- Has Default Pwd (e.g. TRUE or FALSE)
- Has Blank Pwd (e.g. TRUE or FALSE)
- Uses DES Keys Only (e.g. TRUE or FALSE)
- Has Missing AES Keys (e.g. TRUE or FALSE)
- Pwd Rev Encrypt (e.g. TRUE or FALSE)
- Pwd Not Req (e.g. TRUE or FALSE)
- Pwd Never Expires (e.g. TRUE or FALSE)
- Has Shared Pwd (e.g. TRUE – Domain Shrd Pwd Grp x Of y or FALSE)
- Compromised Pwd (e.g. TRUE or FALSE)
- Most Used Hash (e.g. <hash> (<count>) or N.A.)
–
When the script finishes, it produces a CSV report that contains every account in the AD forest that can authenticate (user, computer, gMSA, inetOrgPerson) and potentially be a threat, and it displays that CSV in a GridView automatically. The CSV can of course also be used in Excel if needed. With this information you may be able to remove or fix configurations and/or get an idea how things look like to mitigate risks as much as possible!
While the script is running it logs every to a log file. which is in the same folder as the script itself.
–
This script requires:
- PowerShell Module: ActiveDirectory
- PowerShell Module: LithnetPasswordProtection
- PowerShell Module: DSInternals
- LithNet Active Directory Password Protection Store With Banned Words And/Or Compromised Passwords/Hashes
- Enterprise Admin Permissions, or at least "Replicate Directory Changes" and "Replicate Directory Changes All" for EVERY NC in the AD forest!
REMARK: Script does check for Enterprise Admin role permissions!
–
Scan/Check All Accounts In The AD Forest And Create The Report
.\Scan-And-Check-All-Accounts-In-AD-Forest_05_Account-And-Password-Hygiene-Info.ps1
–
The script has been tested in three different AD forests:
- AD forest with a Single AD domain with less than 500 accounts and quite some account config
- AD forest with a Single AD domain with approx. 150000 accounts and less account config
- AD forest with Multiple AD domains (Forest Root Domain, Child Domain and Tree Root Domain) with approx. respectively 4000, 25000 and 12000 accounts and less account config
–
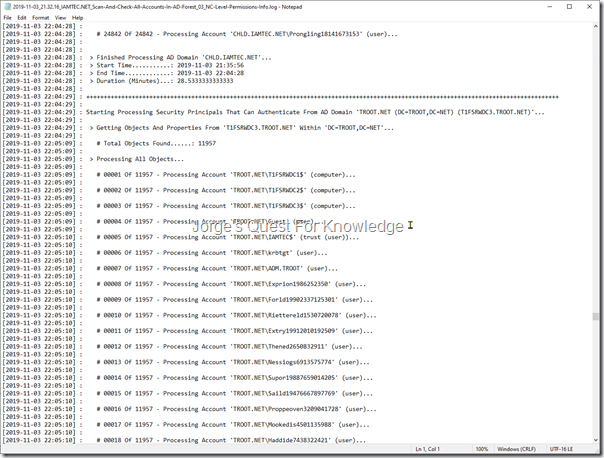
Figure 1a: Sample Output Of The Log File
–
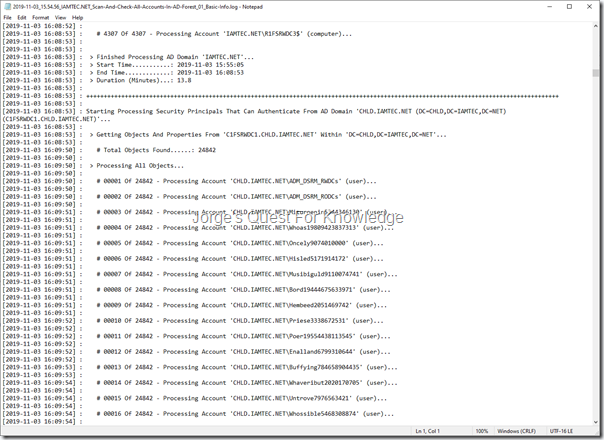
Figure 1b: Sample Output Of The Log File
–
Figure 1c: Sample Output Of The Log File
–
Figure 1d: Sample Output Of The Log File
–
Figure 1e: Sample Output Of The Log File
–
To open the CSV on another computer and display it in GridView, execute the following command:
Import-CSV <Full Path To The CSV File> | Out-Gridview
Figure 2a: Sample Output Of The CSV File Displayed In PowerShell GridView
–
Figure 2b: Sample Output Of The CSV File Displayed In PowerShell GridView
–
To get the script, see: Scan And Check All Accounts In AD Forest – Account And Password Hygiene
–
Cheers,
Jorge
————————————————————————————————————————————————————-
This posting is provided "AS IS" with no warranties and confers no rights!
Always evaluate/test everything yourself first before using/implementing this in production!
This is today’s opinion/technology, it might be different tomorrow and will definitely be different in 10 years!
DISCLAIMER: https://jorgequestforknowledge.wordpress.com/disclaimer/
————————————————————————————————————————————————————-
########################### Jorge’s Quest For Knowledge ##########################
#################### http://JorgeQuestForKnowledge.wordpress.com/ ###################
————————————————————————————————————————————————————-